Taking the worry out of IT
All bases covered, below are the base products delivered to ALL clients using Deep Tech IT Solutions
Remote Support
Fast and effective resolutions to minimize team downtime.
Onsite Support
When it can’t be handled remotely, we come to you!
Portal Access
Create, update and view your tickets.

24/7 monitoring
We are always watching the little things, so you don’t have to.
Flexible Helpdesk
We know your team doesn’t have the time to focus on software upgrades and password resets. Our Service Desk Team can handle all levels of IT support requests for your business. You focus on high initiatives, and we’ll make sure your team has the IT support they need to focus on the tasks at hand.

Help Desk Focus
On Demand Support
- network administration
- application support
- purchasing
- security
- data retention
Managed Services
- device support
- network administrations and monitoring
- application support
- procurement and provisioning
- security
- data retention
- techology and advisory services
- vendor management
- preventative maintenance
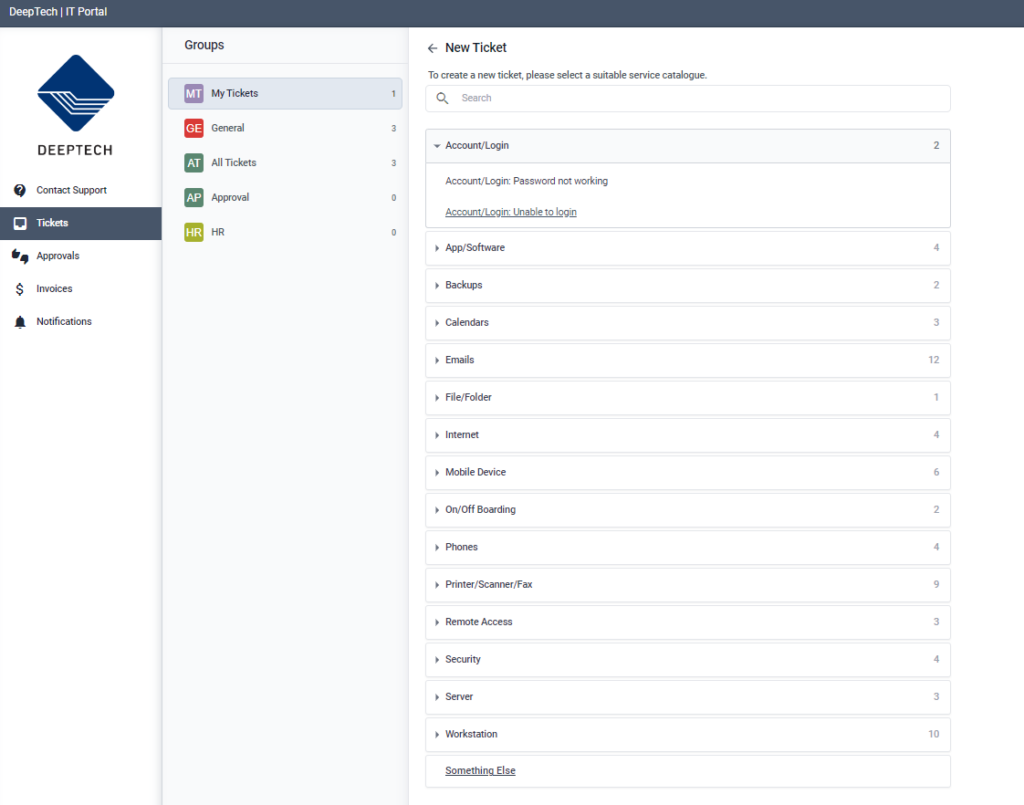
Easy Access
Our IT portal makes submitting a ticket to the help desk a breeze. Simply go to portal.deeptechinc.com, select the issue you have, answer some questions and click submit. You can view your tickets and update the ticket via the portal.
What’s the catch?
No catch, in fact we can work to customize your portal experience to tailor to your business needs.
Procurement and Provisioning
Procurement
During your onboarding, you will work with our Logistics team to determine your equipment needs. We will look at your current equipment, create standards for new hires, create processes for purchasing new hire needs, equipment upgrades, license renewals and miscellaneous purchases.
Provisioning
Logistics
The final cherry on top of the procurement and provisioning process is that our logistics team will deal with the shipping and receiving. Whether it be on your own shipping account or ours, we will track the shipments and alert you as to arrivals and departures of your equipment.
Strategic Projects
Get the support you need for your strategic projects. Put the expertise of our professional services team and a nationwide network of vetted partners to work for you. Every step of the way, from project discovery to scope of work and execution, our dedicated project managers are the best partner to get the job done.
Project Types
Onsite Projects
Email and Data Migrations
Network Builds and Upgrades
Office Buildouts and Moves
and more…
Security & Business Continuity
You no longer have to stress about securing what is essential to your business. DeepTech ensures your team and data are secure and prepared for anything that may come your way.
Security Offerings

Awareness and Training
It may be hard to admit, but anyone can be susceptible to social engineering. Let DeepTech help train your team on what to look out for and what to flag to keep your information safe and secure.

Backups and Encryption
Backups are the last line of defense against attackers. When was the last time you tested your backup solution?
Compliance
Providing remediation and security hardening through audits (HIPAA, ISO, SOC2, PCI, HITRUST, etc.) from our partners or yours.
Malware Protection
The average data breach costs $3.8M, caused primarily by Malicious software, including viruses, adware, spyware, browser hijacking software, etc. Let's prevent them from being activated.
Monitoring
No need to hire a team to monitor your network 24/7. DeepTech partners with world-class Security providers to ensure your computers are monitored and protected.
Multi-Factor Authentication (MFA)
Passwords alone no longer cut it. Over 1 Million passwords are stolen a week, and hacking is becoming increasingly more sophisticated. Enhance your security by requiring your team to identify themselves by more than a username and password.
Patch Management
Ensure your workstations and network are as up-to-date as possible to prevent attackers from exploiting known vulnerabilities.

Never skip a beat
Strong business continuity saves money, time, and company reputation. Businesses that experience an extended outage risk financial, personal, and reputational loss.
Don’t cry over spilled milk
Accidents happen, even milk on a keyboard, luckily, quick restores can save the day. Keeping a current backup copy allows your data to be restored from an earlier point in time to help your business recover from an unplanned event.
- Loss or corruption
- Accidental deletions
- Lost or stolen devices
- Broken devices
- Corrupted data
- Human error


Like a scout, be prepared
Unfortunately, not all disasters are preventable but you can prepare! We create a custom disaster recovery plan to help your business to avoid catastrophic data loss. By outlining strict regiments for your backup and data recovery, the disaster recovery plan ensures that your data isn’t only safe from an attack or outage and handled securely.
Additional Services
App, Cloud & Device Management
Centrally managing all of your software and hardware to ensure your team doesn’t waste productivity on asking for permissions.
Virtual CIO
Building towards your vision requires an expert.
Going above and beyond the function of being a trusted adviser and understanding the technical risk and business impact decisions can make.
Our strategy combines budgeting and planning techniques to recommend solutions while leveraging technical alignment for greater control over your scalability.
Application Management
Each organization uses software in unique ways. We work with you to identify your needs and ensure each application is replaced at a global and workstation level to meet your business goals.
Compliance Consulting
Assess, Review, and Remediate Compliance auditing helps us identify weaknesses in regulatory compliance processes and create paths for improvement. In some cases, guidance provided by a compliance audit can help reduce risk and avoid potential legal trouble or federal fines for noncompliance.
Mobile Device Management (MDM)
Enforcing security controls that meet your organization’s compliance prevents data loss, theft, and malware from affecting your business.



